There is currently an unpatched Windows security flaw that effectively allows an attacker access to anything and everything. It is present in every version of Windows.
 www.theregister.com
www.theregister.com
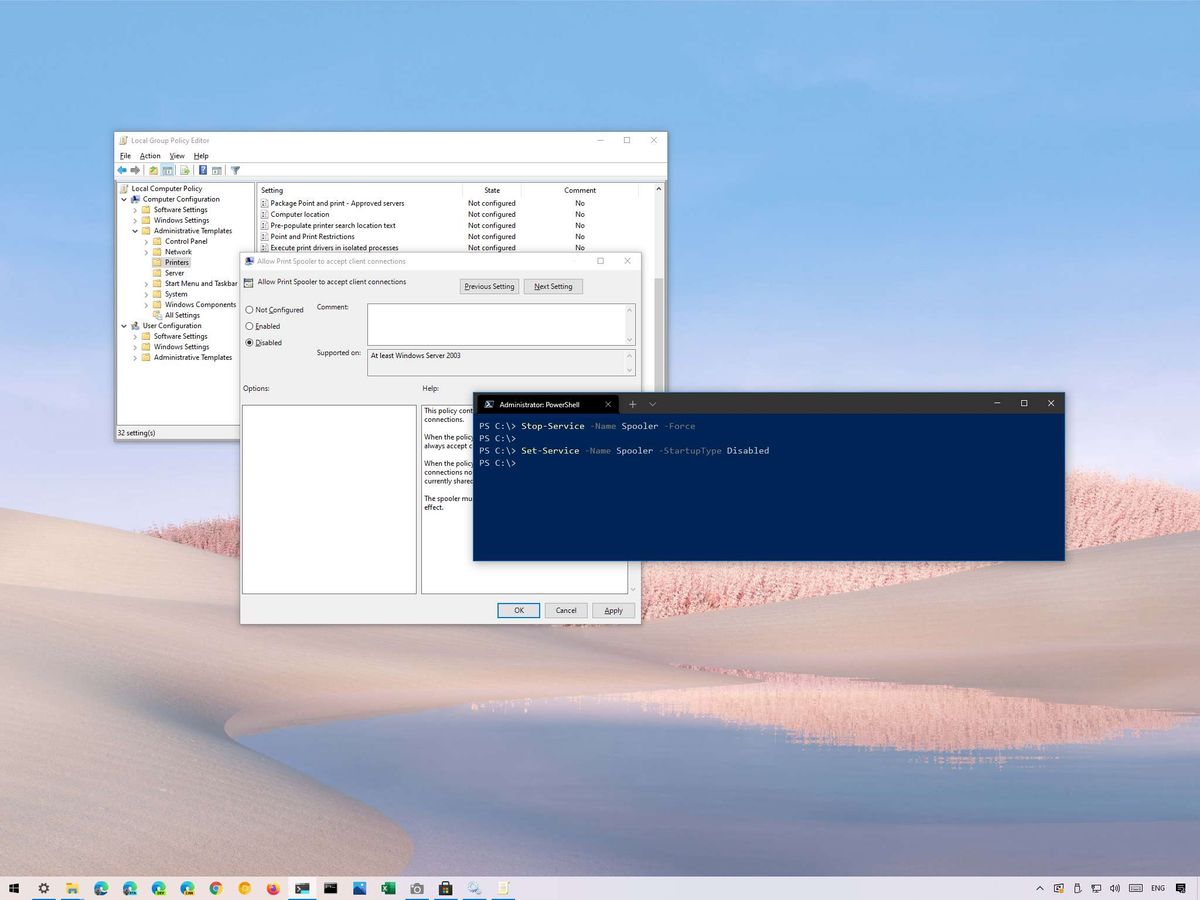
For those who use Windows, this is how you can block the attack until a patch is in place. Unfortunately blocking the attack means disabling printing from Windows machines. The second method described leaves local (i.e. hardwire connecting printer and computer) printing intact and only disables network printing (still a royal pain as most printers are connected via the network).
 www.windowscentral.com
www.windowscentral.com
Hopefully Microsoft gets a patch out pretty quick.
The PrintNightmare continues: Microsoft confirms presence of vulnerable code in all versions of Windows
That printer plugged into your domain controller? Yeah, you might not be using that for a while
For those who use Windows, this is how you can block the attack until a patch is in place. Unfortunately blocking the attack means disabling printing from Windows machines. The second method described leaves local (i.e. hardwire connecting printer and computer) printing intact and only disables network printing (still a royal pain as most printers are connected via the network).
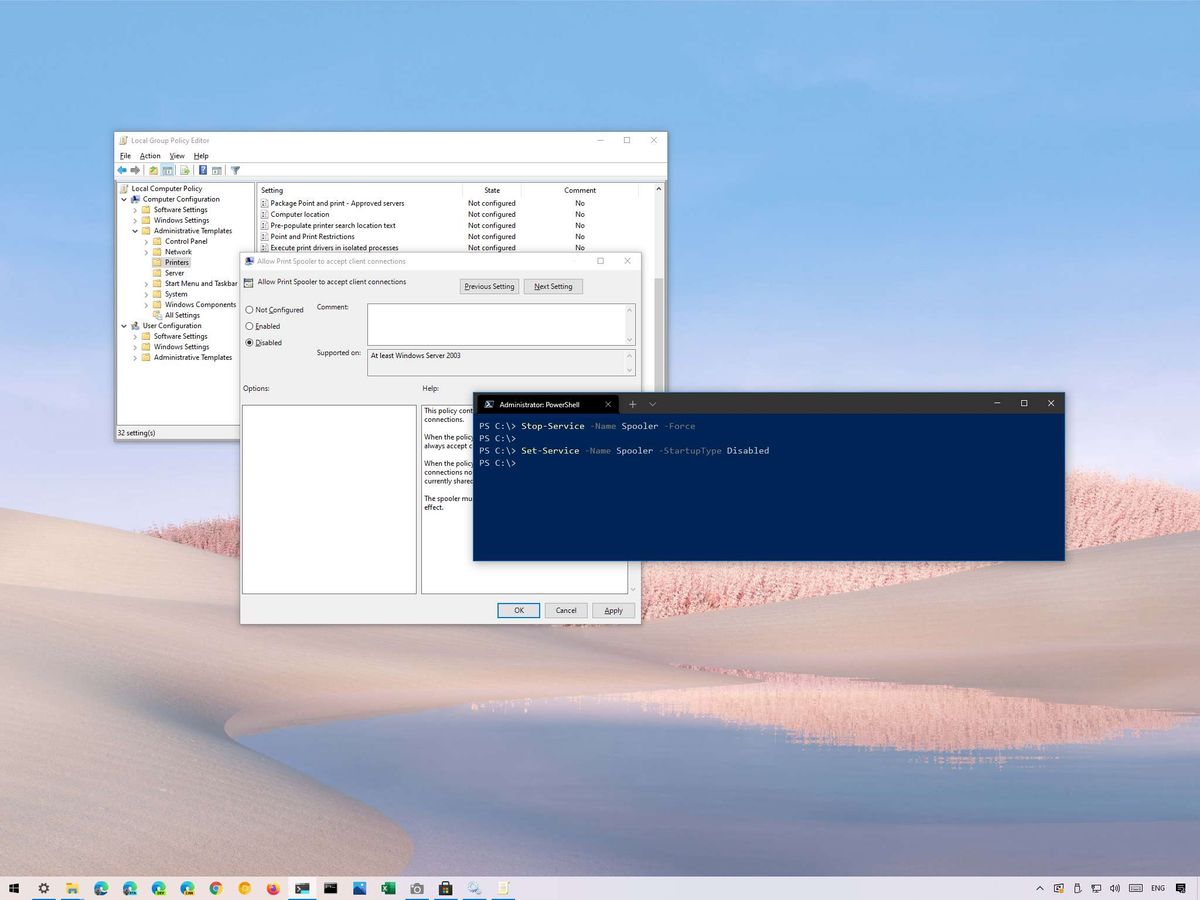
How to mitigate Print Spooler PrintNightmare vulnerability on Windows 10
An unpatched vulnerability could open the doors for attackers from accessing your device — here's how you can protect yourself until a permanent fix is released.
 www.windowscentral.com
www.windowscentral.com
Hopefully Microsoft gets a patch out pretty quick.
